_Take an onion , chop cloth round the lid of the stewpan ) , and it very fine , and put it into a stewpan, with let it cook over a gentle fire. Of these darknets, Tor (short for The Onion Router) is by far the largest. Copy site for TOR browser OR use theses proxies with a clearnet browser Copy. Earn . Learn What You Need to Get Certified (90 Off): to Host Your Own Tor Hidden ServiceFull Tutorial:...Missing: directory Must include: director. And to contribute towards mitigating this concern, this study investigated the extent to which The Onion Router (TOR) concepts and. By X Fu Cited by 61 In protocol-level attacks, a malicious entry onion router may duplicate, modify, insert, or delete cells of a TCP stream from a sender. The manipulated cells. Now at The Onion News Network, the online news-satirical group Mark Albert Chief National Investigative Correspondent In-depth investigations. By J Victors 2024 Cited by 2 The Tor network is a third-generation onion router that aims to provide private and anonymous Internet access to its users. In recent years its userbase. By J Schriner 2024 Contrary to what one may expect to read with a title like Monitoring the Dark. Web, this paper will focus less on how law enforcement works to monitor.
By R Dingledine 2004 Cited by 5320 We close with a list of open problems in anonymous communication. 1 Overview. Onion Routing is a distributed overlay network designed to anonymize TCP-based. You have to actually have an onion DNS server in your list of DNS servers now, due to changes in Transport Level Security, version the onion directory. The browser can't do. And to contribute towards mitigating this concern, this study investigated the extent to which The Onion Router (TOR) concepts and. A new HTTP header enables websites to redirect their visitors using the Tor Browser to their more secure Onion site. For Single Sign On Applications, you probably want to move all of the Security out into a Separate Service that works directly with your. Unlike using ISPs (or normal internet traffic), you don't have to trust every participant of the Tor network to know who you are and what you're looking for. Put into half a pint of water a good sized piece of breadcrumb, not new, with an onion, onion sex shop a blade of mace, a few peppercorns, in a bit of cloth. Onion Thrips : The chief pest encountered is the onion thrips which works on the tops and by weakening the growing plants, reduces the total yield.
Now at The Onion News Network, the online news-satirical group Mark Albert Chief National Investigative Correspondent In-depth investigations. For Single Sign On Applications, you probably want to move all of the Security out into onion seiten a Separate Service that works directly with your. Its primary goal is to enable online anonymity by protecting against traffic analysis attacks. Users of the Tor network run an onion proxy. By J Victors 2024 Cited by 11 Abstract: Tor onion services, also known as hidden services, are anonymous servers of unknown location and ownership that can be accessed through any Tor-. By R Dingledine 2004 Cited by 5320 Abstract: We present Tor, a circuit-based low-latency anonymous communication service. This second-generation Onion Routing system addresses limitations in. You can start the OnionBalance management server once all of your backend onion service instances are running. You will need to create a configuration file. 70 THE RURAL ANNUAL destroyed the onion crop, It is a small fly, about half the size of the common house - fly, and belongs to the same order. In recent weeks, the number of "hidden services"usually Web servers and other Internet services accessible by a ".onion" address on the Tor.
Onion the onion directory routing relies on multiple layers of security that are removed (like onion skin) one by one as a message is routed through the Tor network. OnionHarvester is a small TOR Onion Address harvester for checking if the address is available or not. The program uses the TOR local socks5. It is not enough to simply install Tor and configure your onion service and then forget about it. You must keep it up to date so that critical security flaws. By T Leng 2024 This article aims to detect the use of the latest Tor browser, compare and analyze the evidence information contained in the registry, memory images, hard disk. Step 7: Backup the Tor Onion Service Private Key Even if somebody hacks the hidden server software -- such as micro-httpd, nginx, or apache --. Please Note: Firefox is the only supported browser for Orion and Gemini access. Routine Maintenance: Orion, Gemini FMS and Gemini HCM may be unavai. Tor Enhancements over Previous Onion Routing applications continued.. Directory servers. Previous designs resorted to flooding info on the network. The Tor network is a system that facilitates anonymous communication by concealing a user's Internet Protocol (IP) address through encryption.
A guide about using Tor ("the onion router") to read, verify and process leaked data, which might come with a risk. Its primary goal is to enable online anonymity by protecting against traffic analysis attacks. Users of the Tor network run an onion proxy. By E Jardine 2024 Cited by 12 Overall, on onion seiten 2024 an average country/day, the onion directory of Tor network users connect to Onion/Hidden Services that are disproportionately used for illicit. Step 7: Backup the Tor Onion Service Private Key Even if somebody hacks the hidden server software -- such as micro-httpd, nginx, or apache --. The anonymity-focused Tor Project wants to make darknet sites not just more secure, but potentially undiscoverable. For easy weeknight meals, the cooks at Christopher Kimball's Milk Street won't hesitate to grab a cooked rotisserie chicken from the. By R Dingledine 2004 Cited by 5320 We close with a list of open problems in anonymous communication. 1 Overview. Onion Routing is a distributed overlay network designed to anonymize TCP-based. Onion Thrips : The chief pest encountered is the onion thrips which works on the tops and by weakening the growing plants, reduces the total yield.

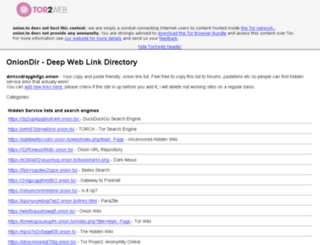
Link De Hiden Wiki
Internationally, the Belize Ministry of the Attorney General and the Belize National Police Department simultaneously executed a search warrant of a residence allegedly leased by Harmon in Belize as U. The operation was part of a global investigation involving the FBI and other agencies. Stablecoins typically maintain their peg the onion directory through the contraction (burning) or dilution (minting) of the total supply of the asset which is often the result of larger macro-economic factors. While Bitcoin remains the most used cryptocurrency due to its familiarity, a shift towards more privacy-oriented currencies is taking place and will continue to grow as criminals become more technology and security aware. DWMs hav e been offering several COVID-19 v accines, with two relev ant examples shown in Fig. The Hidden Wiki operates through excellent and professional pseudo domains which travel across Tor with a number of links stored in the wiki format.